Implementing a Robust Cybersecurity Framework in Education: A Case Study from a Leading Toronto College
Case Study: Creating A Safer Learning Environment With MXDR
Case Study: Treating Ransomware Breach Face with Difenda MXDR
Case Study: Architecting Security Environments for Unique Hybrid-Cloud Networks
Case Study: Building a Cybersecurity Program From The Ground Up
Case Study: Microsoft IP & G
Case Study: Regaining Your Safety Posture After a Cyber Attack
Case Study: E2E Microsoft Security Roadmap
Case Study: Building a Proactive Security Program from Start to Finish
Case Study: Gaining Visibility into the OT Environment
Case Study: Achieve A Truly Co-Managed and Collaborative Security Program
Case Study: Difenda MDR & Managed SIEM
Making the Case for the Consolidated Security Stack: A Quick Overview
Defender for Office 365 Professional Service
Defend cloud applications and database infrastructure from account compromise, insider threats, and access misuse. Keep your cloud environment safe and secure with built-in defence from your business environment to the Azure Cloud Platform.
Defender for Identity Professional Service
Identify potential compromises to user identities and fortify your Active Directory environment with our customized Microsoft Defender for Identity Professional Security Services. Mitigate the risks associated with anonymous IP address use and password spray to better protect your network.
Defender for IoT Professional Service
From consulting to design and implementation, monitoring, maintenance and training services, our team of experienced experts deliver holistic cybersecurity programs to help maintain your cyber defenses over time.
Managed SIEM
Cut through the noise with managed SIEM for Microsoft Sentinel. When you combine Microsoft Sentinel and the strength of Difenda’s highly trained teams, you can attack the chaos of SIEM alerts with context. Our team of expert analysts continuously tune Microsoft Sentinel to eliminate false alarms, enable rapid identification of emergent threats, and align with your organization’s unique threat landscape.
Managed Endpoint Threat Detection and Response
MXDR for OT
Turn-key agentless extended detection and response (XDR) that is rapidly deployed, works with diverse endpoints, IoT, OT, and industrial control system (ICS) devices.
Defender for Endpoint Professional Service
We provide end-to-end support – from design and deployment to validation and training, enhancing your endpoint security capabilities with improved visibility and tiered alerts.
Sentinel Professional Services
Our professional security services for Microsoft Sentinel are tailored to meet your organization’s needs today and in the future. Benefit from our certified and highly skilled Microsoft Security experts who will support you every step of the way, from designing to implementing and deploying Microsoft Sentinel.
End to End Security Roadmap
Get a roadmap that guides your Microsoft Security implementation. With a Microsoft optimization roadmap alongside technical security design from Difenda experts, you get clarity that guides your daily and long-term defense operations.
Is Your Sentinel Keeping Score
Education
Manufacturing
Achieving Proactive Cybersecurity: A Guide for Executives
Strengthening Your Security Posture with Data Governance
What are the Key Benefits of a Security Operations Center? SOC Benefits Explained
Video: Difenda and Microsoft Join Forces to Reduce Alerts for the City of Brampton
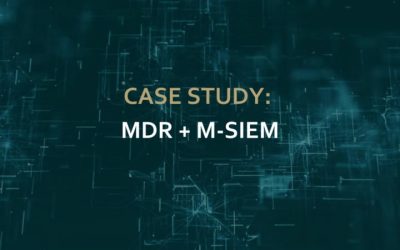
Difenda MXDR Deployment Process
What is Microsoft Managed XDR (MXDR)?
What Is Endpoint Detection and Response? EDR Security Deep Dive
A CISO’s Guide to Communicating Cybersecurity to The Board of Directors
11 Cybersecurity Awareness Tips
What is SOC-as-a-Service? Exploring Managed SOC Offerings
The High-Tech Gangsters of Organized Cyber Crime
How Cyber Threat Intelligence Can Guide Threat Hunting – And Should.
Purview Professional Service
We help implement and optimize your Purview. Our services includes data discovery, lineage, classification, privacy, metadata management, security, and more.
Remote Incident Response
Let Difenda Remote Incident Response handle your cyber breach management. With proactive ransomware mitigation support, ransomware attack response services and digital forensics services, you’ll be back to business as usual in no time.